FACULTY HOME
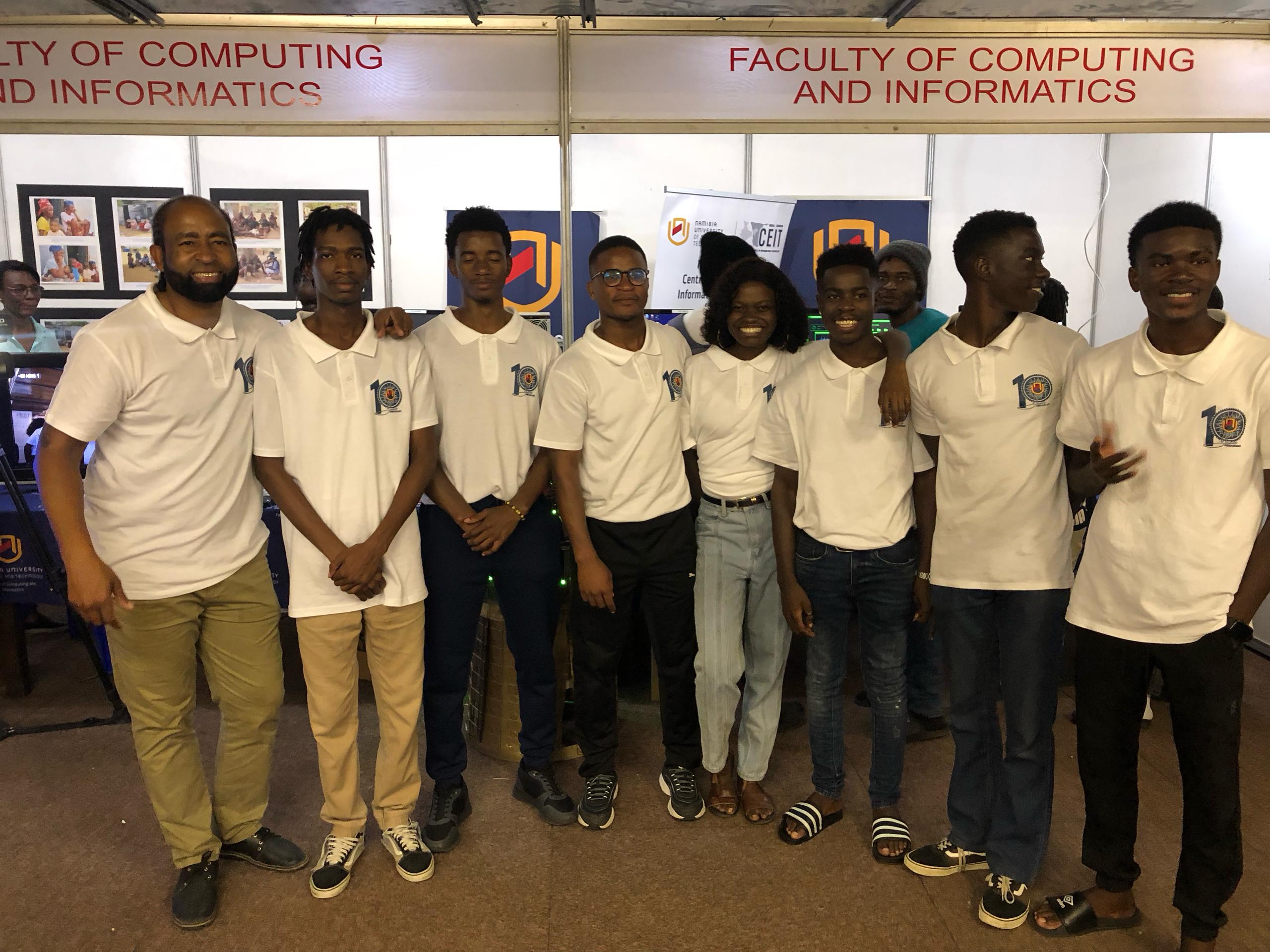
The Faculty of Computing and Informatics offers different specialisations and different exit levels. Our offering includes Bachelor, Bachelor Honours, Master and PhD degrees in various specialisations in Computer Science and Informatics. We also offer Postgraduate Certificates in specialised fields. We endeavour to keep up with the rapid changes and evolution of technology. We produce high-quality graduates for both the local and international ICT sectors. We are further renowned for innovative projects and research. We have active research clusters and strive to solve national and international problems by using ICT as an enabler to societal digital transformation. We also consider community service as a priority.
Our research addresses the needs of the country, the region and the world at large. The Faculty focuses on four main research areas: Big Data, Indigenous Knowledge in Digital World, Smart & Secure Environment and Digital Transformation.
We have the following research clusters: Indigenous Knowledge Management Systems (IKMS), Dependable Advanced Network Systems (DANS), Marginalised Community Development (MCD), Smart Communication Systems (SCS), Digital Forensics & Information Security (DFIS), E- Participation (EP) and Business & Policy Analytics (BPA).
Informatics
- Data Science
- Informatics
- Web Informatics
- Health Informatics
- Information Technology
SAP Academy
Software Engineering
- Software Engineering
- Human Computer Interaction (HCI)
UX/ Interaction Technology Lab
Cyber Security
- Cyber Security
- Digital Forensics
- Information Security
- Systems Security
- Network Security
- Software Security
Cyber Defense Lab
Checkpoint Secure Academy
Fortinet Academy
Computer Science
- Computer Science
- Computational Sciences (AI)
- Communication Networks
- System Administration
Cisco Networking Academy and Instructor Training Centre
Oracle Academy
Robotics Lab
Journalism and Media Technology
- Journalism and Media Technology
- Advanced Journalism Studies (Investigative/ Data/ Science Journalism)
- Multimedia Design and Production
- Public Relations and Advertising
- Creative Media/ Production House/ Lab, Echoes News Service
Digital Arts and Animation
- TV and Film Production
- Cinematography
- Digital Advertising
- Motion Capture / TV and Film studio/ Luno Pictures Hub/VFX and AI

%20of%20the%20ImpactLab%20Hackathon%202025.jpg)
%20with%20the%20Second%20Place%20Winners%20(Feed%20Forward%20Namibia)%20of%20the%20ImpactLab%20Hackathon%202025.jpg)